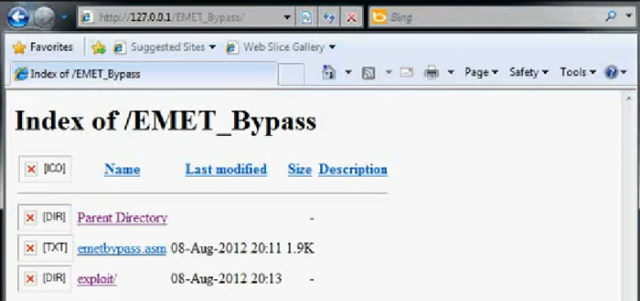
A computer's Internet Explorer screen just prior to it being exploited by an attack that bypasses new protection baked into EMET. Real-world attacks would conceal this behind-the-scene view.
Two weeks after Microsoft released a free utility designed to help its software better withstand a powerful hacking technique, a security researcher has demonstrated an exploit that bypasses the newfangled protection.
Microsoft released a new version of its Enhanced Mitigation Experience Tool on July 24 to great fanfare. The update to EMET, which adds an extra layer of defense to prevent vulnerabilities from being successfully exploited, introduced protections designed to block an advanced attack technique known as return oriented programming. A regular staple in exploits at the annual Pwn2Own hacker contest, ROP works by rearranging benign pieces of code already present in memory to form a malicious payload. The new protection, known as ROPGuard and developed by University of Zagreb researcher Ivan Fratric, fetched a $50,000 prize under a security contest Microsoft sponsored.
On Thursday, a security researcher whose Twitter profile claims he's based in Iran said he had bypassed the ROPGuard protections. A video demonstration accompanying his blog post showed a Windows 7 machine falling prey to a ROP-induced exploit even though the OS was running version 3.5 of EMET. The anti-ROP mitigations work by wrapping certain important system functions with extra code to verify that they're not being called by attack code. Based on a brief technical description, the attack circumvents this protection by calling the system function directly, thereby bypassing the protective wrapper.
Read 7 remaining paragraphs | Comments
No comments:
Post a Comment